Commanders now responsible for cybersecurity training after Army cuts online course requirement to once every 5 years
The Army reduced the frequency of mandatory cybersecurity training to once every five years, according to a policy that went into effect late last month, axing an annual requirement and making individual commanders responsible for preparing their personnel for digital defense.
The move followed a Sept. 30 memo by Defense Secretary Pete Hegseth directing the military to reduce the time personnel spend on cybersecurity training, with the aim of “enabling our warfighters to focus on their core mission of fighting and winning our Nation’s wars without distraction.”
Five months later, the Army codified its reduction for training it said was ineffective. Now, commanders are responsible for preparing their soldiers and civilians on cybersecurity, according to a senior service official who said the change was intended to give unit leaders more flexibility.
“Commanders are now responsible for assessing the specific cyber risks to their mission and tailoring their unit’s training accordingly,” said Army Chief Information Officer Leonel Garciga in an emailed statement to DefenseScoop Friday. “This allows them to integrate cybersecurity into their operational training plans in a way that is relevant and effective for their soldiers.”
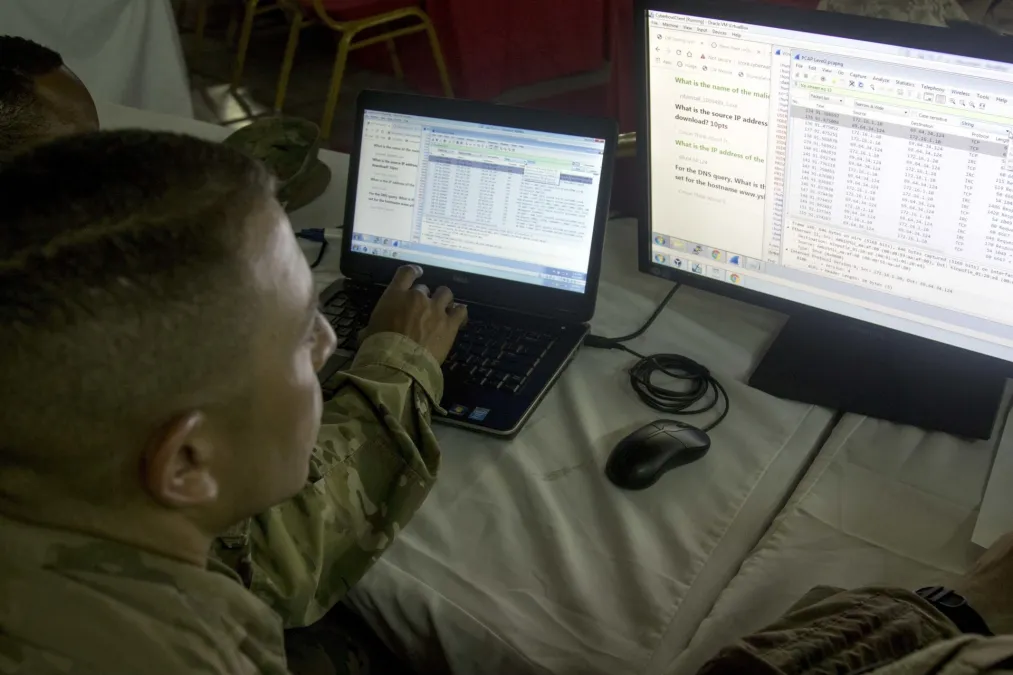
Cybersecurity experts who DefenseScoop spoke to, both of whom are veterans, said greater command responsibility over digital protection was positive, but they varied on how the Army’s new tack would be implemented. One warned that leaders not already focused on the digital domain likely won’t dedicate time for cyber training beyond their unit’s primary mission.
Without a yearly requirement, continuity between leadership changes becomes increasingly vital. Both emphasized how critical cybersecurity has become given a changing, high threat environment during the Iran war, and amid constant digital incursions from other state actors such as China and Russia.
The annual Defense Department training, called the Cyber Awareness Challenge, would not have adequately prepared troops for those threats, according to one of the cyber experts. The success of the Army’s new program — which also leans on web-based training — remains to be seen, and hinges on commanders’ ability to implement it effectively.
The service publicized the Feb. 27 memo about the initiative on Thursday as the U.S.-Israeli war with Iran marked its fourth week. The conflict has set off multiple digital attacks on American entities from Tehran-linked proxies and heightened warnings from experts over cybersecurity.
Retired Rear Adm. Mark Montgomery, senior director of the Center on Cyber and Technology Innovation at the Foundation for Defense of Democracies, said that a once-every-five-year cyber requirement “is unusual and probably a little riskier than one would expect in an agency that’s under constant foreign adversary attack.”
Top officials have said military operations under the Trump administration over the last year have ushered a “cultural shift” for the digital domain as U.S. cyber entities become increasingly involved in those missions. Iran, regarded by federal agencies as having a capable “hacktivist” network, has wrought its own cyber turmoil against the U.S. in recent weeks.
Medical device manufacturer Stryker reported a cyberattack earlier this month that wiped company data, and a Tehran-affiliated group said it carried out the strike. The same Iran-linked hackers reportedly accessed FBI Director Kash Patel’s personal email last week, posting some materials online. The bureau is offering a $10 million reward for information that leads to information about the group, known as the Handala Hack, or Handala.
Beyond direct attacks, the war has flushed the online space with confusing or outright false information that can directly affect service members. Experts said that cybersecurity is often viewed too narrowly, but is closely tied to information warfare by adversaries that’s been made increasingly easy with AI and cryptocurrency.
Just days after the conflict began, DefenseScoop reported about a suspicious message circulating in units across the force and on social media. The message purported to be from U.S. Cyber Command, warning troops to turn off location services and that multiple commercial apps were compromised.
While the origin of the message remains unclear and has not been tied to nefarious actors, officials told the publication that the command never sent it. It spread through various official and unofficial military channels, causing confusion over its authenticity within the ranks.
Garciga said that the service’s latest approach to cyber training is geared toward the slew of complex threats emanating from the war.
“The Army’s new approach is specifically designed to be more agile and effective in heightened threat environments like the one surrounding Operation Epic Fury,” Garciga said. “Rather than relying on a one-size-fits-all annual training model, empowering commanders allows for a more rapid and tailored response to emerging threats.”
He said that, for example, if intelligence detects increased phishing attacks or social engineering threats related to the operation, commanders can “instantly direct their unit to conduct targeted training on that specific threat.”
Moving away from the ‘butt of all jokes’
While the baseline requirement for the military’s Cyber Awareness Challenge — which has long been the “butt of all jokes” among troops, according to one cybersecurity expert — is every five years for the Army, Garciga said, commanders can decide to employ “more frequent or specialized” training based on their units’ situation, systems or “threats they face.”
Montgomery said units already focused on cyber may embrace the new directive to tailor such training for their own personnel and operations, but those that aren’t likely won’t. Infantry or armor units, for example, are already busy with tasks related to their core roles.
“That’s not going to happen,” he said. “If you have extra training time, you usually apply it to your primary mission.”
Many soldiers who have been forced to click through online training will likely welcome slashing the Cyber Awareness Challenge, which for years saw virtual avatars named Tina and Jeff quiz troops through various scenarios related to phishing scams, ID protection and network security, for example.
Garciga said the change shed a “compliance-based, check-the-box exercise” for a program that “trusts our leaders on the ground to make informed decisions, ensuring our soldiers’ time is spent on training that directly contributes to their readiness and lethality, rather than on redundant administrative tasks.”
Retired Col. Sarah Cleveland, a former Air Force cyber officer and senior director of federal strategy at ExtraHop, said yearly online courses couldn’t keep up with how quickly digital threats are forming, and a new generation of tech-savvy troops is likely more attuned to the cyber risks they’ve grown up around online compared to older counterparts.
“The threat vectors and the threat surface are so big and changing so quickly that to think annual training is going to prepare somebody for that is crazy,” she said. “I think this is part of the whole work smarter, not harder [philosophy] — use the smart people that you have, empower them to do their job.”
For its part, the Army “found no relational improvement difference in cybersecurity outcomes between the annual training and other less burdensome forms of awareness,” according to Garciga. He said the new method means cyber training is not separate, but “built into the fabric of our operational readiness.”
How commanders work cyber training into that fabric, how they standardize it after they leave leadership, and how the Army will track outcomes of this new program down the line could prove consequential.
Garciga pointed to “a robust catalog of cybersecurity resources that commanders can leverage at any time to meet their specific needs,” but did not specify which resources he was referring to. Army spokesperson Maj. Sean Minton said that catalogue included cyber courses on the Joint Knowledge Online, or JKO portal. That training is also web-based, as the name suggests.
Montgomery said the annual course had the opportunity to be effective, but online training in general doesn’t work well without hands-on instruction from dedicated staff.
“With online training, the effectiveness is in the hands of the customer,” he said. “That’s always a risk, whether it was a five-year periodicity, one-year periodicity, whether the [commanding officer] is responsible or the big Army’s responsible — in all cases, there is a risk with online training that people who just aren’t interested remain not interested.”
Both Montgomery and Cleveland noted that continuity could prove to be a difficult factor under the new program. Commanders rotate out of leadership often (more frequently than the five-year online training requirement), meaning one leader might view cybersecurity as less important than the previous one and therefore not prioritize it.
And while ineffective at combatting evolving cyber risks, according to Cleveland, annual training provided a semi-frequent touchpoint for services to assess a level of cyber readiness and its correlation to digital threats. How the Army intends to track the outcomes of the new program was unclear.
“This strategy ensures that our cybersecurity posture is not static,” Garciga said. “It is an active, operational function of command that is directly tied to the mission. By giving commanders the autonomy to manage cyber risk, we enable them to better protect their formations and increase their lethality in any environment, especially when the cyber threat is high.”






