Air Force CIO: Zero trust enhances speed and simplifies environments to work with allies, joint partners
As the Defense Department develops its concept of operations for more joint, sensor-and-data-driven warfare, the application of zero trust will be key in enabling the U.S. to more quickly share information and simplify connections with allies and partners, the Department of the Air Force’s CIO said Wednesday.
DOD and the military services are working in lockstep under the guidance of a recently issued strategy to adopt a zero-trust architecture for cybersecurity across the military enterprise. Through this vision, they aim to constantly monitor users and devices on department networks, rather than letting them roam free once they’re granted access to a network, which is the case with existing models of perimeter defense where networks are often siloed and over-segmented to protect various data.
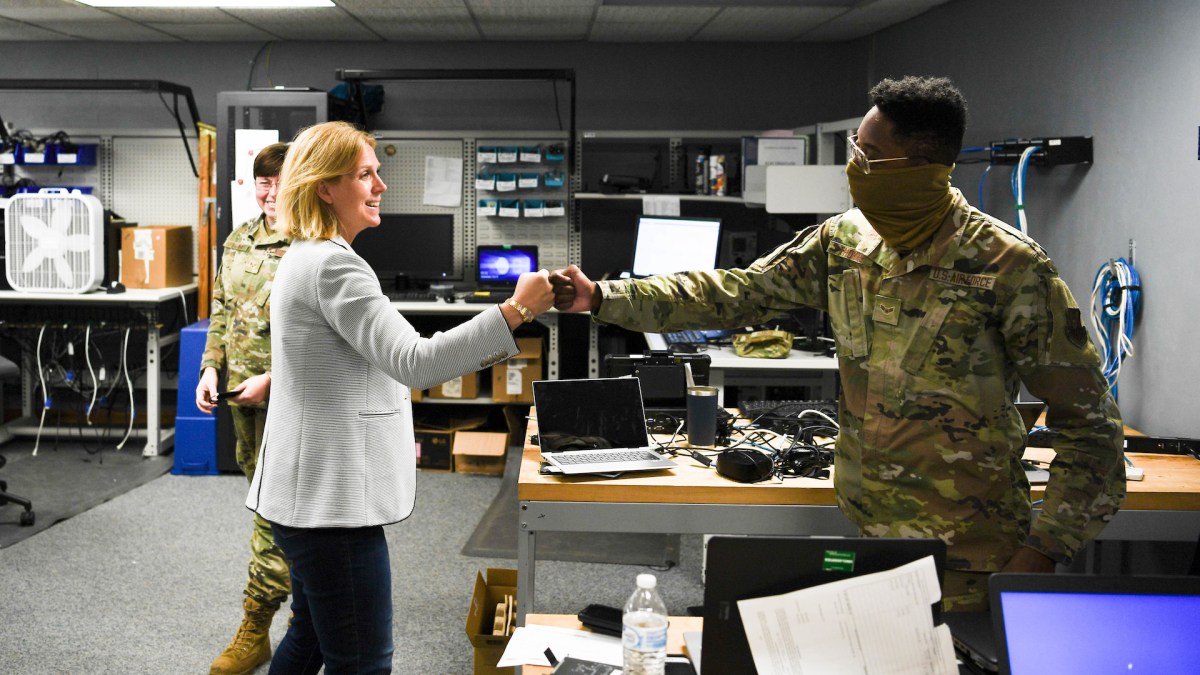
Typically, zero trust is discussed as a modern concept for protecting data from adversaries who may already be on a network. But Air Force CIO Lauren Knausenberger argued it could also be an enabler of speed and simplicity as the military services look to interoperate with one another, companies from the defense industrial base, and global allies.
“The reason that zero trust is so incredibly important in a warfighting construct is that we want to get to a world where we can fight in one environment with our joint partners, our partners and our allies. We don’t want to be logging into 22 different networks to try to talk to 22 different people — we can’t be in an [air operations center] with people having different access to different things and having to log into different machines and redact documents and run up and down stairs,” Knausenberger said during a Mitchell Insitute event Wednesday.
“Zero trust, we recognize, is one of the most dear capabilities to the future fight. Not because it’s, you know, cool tech — it is cool tech — but because it allows us to simplify our environment, and it makes us inherently more secure.”
Air Force CIO Lauren Knausenberger
“That is not the speed of kill chain … that’s going to help us win. And so zero trust is a core principle of getting to that future world where we can fight together with our joint partners and our allies because zero trust inherently looks at the identity of the person — who are you? — or the nonperson entity, and constantly challenges that person, also looks at the data [to determine] should you have access to this piece of data? What about this piece of data? And are you allowed to have access to this piece of data perpetually or just for this moment in time?” she said.
Knausenberger compared the current model for network security to that of a movie theater where once someone is admitted in, they really aren’t monitored and could, in theory, go watch a movie they didn’t buy a ticket for or stay for more showings.
“As long as I see your ticket, you can go on in. I might not know if it’s a forged ticket, maybe you snuck in behind someone else, maybe you snuck in a back door when someone opens it up,” she said. “But once you’re in the theater, I kind of leave you alone … you can go see four movies that day if you feel like it.
But in a zero-trust model, a user’s ticket is getting checked to make sure they’re where they’re supposed to be.
Knausenberger, using the analogy, said that would be “a little bit annoying” to constantly interrupt a patron’s viewing to check their ticket, but added that “with automation [it] would not be.”
“I’m not interrupting your movie in zero trust. Because I have automation happening behind the scenes, you don’t see it. It is seamless to you,” she explained. “But I know that you were there before because you were supposed to be. But it’s because I inherently don’t trust you. It’s because I’m constantly asking. If we do that with every piece of data across our enterprise, it’s pretty hard [for adversaries] to maintain perpetual access across our networks.”
And in turn, it means in the joint warfighting concept, things can be simplified, Knausenberger said.
“I don’t have to do whitelisting, I don’t have to block certain things and allow certain things. I equally distrust everything, but I can very easily validate what is happening,” she said. “And so what I can start to do is, maybe I don’t need an unclassified environment and a secret environment. Maybe I have one environment where things are segmented enough, where I can just see what I can see. I don’t have to worry about logging into two different places. My partners in that AOC, we’re all there fighting together. I don’t necessarily have to stand up a separate network. So I control it so that I can share everything that I need with my allies there.”
Knausenberger explained: “So for a lot of that reason, zero trust, we recognize, is one of the most dear capabilities to the future fight. Not because it’s, you know, cool tech — it is cool tech — but because it allows us to simplify our environment, and it makes us inherently more secure.”






