DDS rolls out new website to help Pentagon scale bug bounties, attract cyber talent
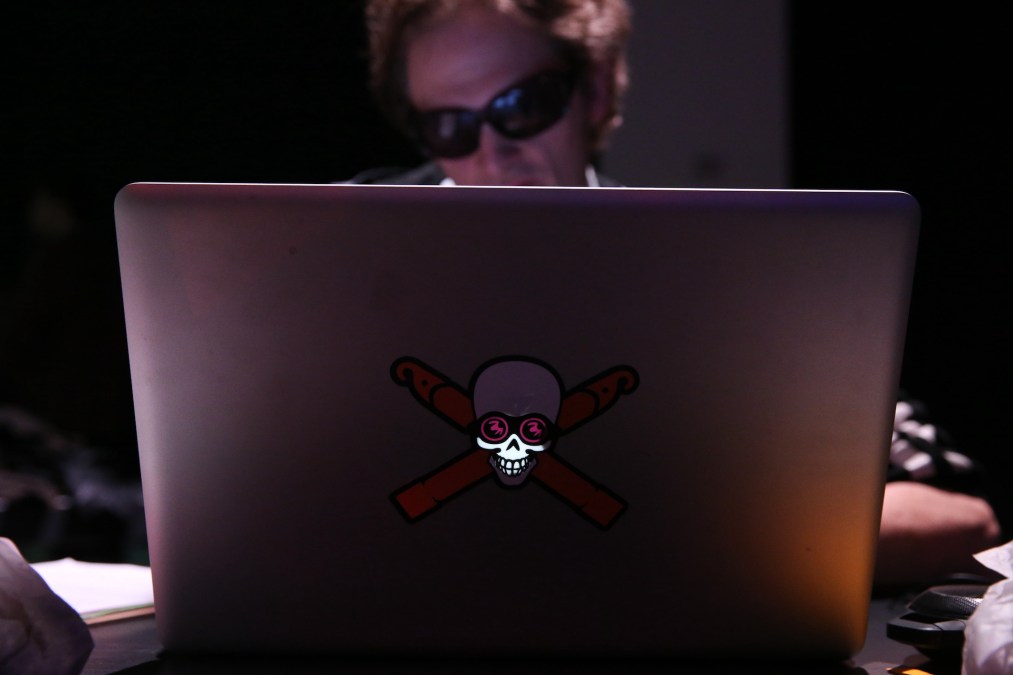
The Defense Department’s Directorate for Digital Services (DDS) has created a new website to complement its “Hack the Pentagon” program and attract new cyber talent.
Hack the Pentagon initiatives leverage white hat hackers who receive monetary rewards or “bug bounties” for finding and reporting vulnerabilities in the department’s public-facing digital systems. The intent is to help DOD components improve their cybersecurity with the aid of outside experts who flag weaknesses for them.
DDS, which has been folded into the new Chief Digital and AI Office (CDAO), launched the program during the Obama administration, and officials have been touting the benefits.
Since 2016, it has overseen more than 40 bug bounties with participation from about 1,400 “ethical hackers” who have collectively flagged more than 2,100 vulnerabilities for remediation, according to a Pentagon press release Thursday. The new website is intended to scale these efforts.
“With the HtP website launch, CDAO is scaling a long running program, which historically offered services on a project-by-project basis, by offering the Department better access to lessons learned and best practices for hosting bug bounties,” Chief Digital and Artificial Intelligence Officer Craig Martell said in a statement. “The website helps equip DoD to run continuous bug bounties as part of a larger comprehensive cybersecurity strategy.”
Another motivation for the rollout is to boost the Pentagon’s ability to bring more cyber talent into the fold, the release noted.
The Defense Department and other federal agencies have struggled to compete with the private sector for cybersecurity professionals. Bug bounties are a way for the DOD to leverage the know-how of people who aren’t employees of Uncle Sam.
“Through Hack the Pentagon, we’re building a global talent pipeline for cybersecurity experts to contribute to our national defense outside of traditional government career paths,” acting DDS Director Jinyoung Englund said in a statement.
The new website includes information tailored to DOD organizations, vendors and security researchers who are interested in participating in the Hack the Pentagon program.
“While advanced tools and automation can be helpful, we believe humans remain essential in defending against cybersecurity breaches. As we shift from an information to an intelligence age, the winning blow will be dealt by humans supported by intelligent machines,” Englund wrote in an online post. “This is why we intentionally invite hackers to break into our systems and assets. By incorporating bug bounties into our overall cybersecurity strategy, we’re updating the cybersecurity playbook to assume breach and think like an adversary.”
In addition to bolstering its own cybersecurity, the department has been exploring ways to help defense contractors better protect themselves. Last year, it wrapped up a 12-month Defense Industrial Base-Vulnerability Disclosure Program (DIB-VDP) pilot project in which it invited members of the defense industrial base to accept vulnerability disclosures for their public-facing systems. In total, 41 small- and medium-sized defense contractors participated in the pilot, and researchers submitted 1,015 reports, of which 401 were validated by system owners for remediation.
Vulnerability disclosure programs differ from bug bounties in that there are no financial rewards for finding weaknesses in digital infrastructure, among other rules.
Updated on March 30, 2023, at 4:10 PM: This story has been updated to include additional comments from DDS’ Jinyoung Englund.






