Navy releases cyberspace superiority vision
The Navy on Wednesday officially released its Cyberspace Superiority Vision, which outlines how the service will stay ahead of adversaries and threats through three main pillars: secure, survive and strike.
Officials, such as Chris Cleary, the principal cyber advisor, have been previewing the plan for some time.
Cleary, speaking Wednesday at the Trellix Cybersecurity Summit, noted that the vision is in line with the Navy Chief Information Officer’s information superiority strategy released about three years ago. That strategy aims to ensure the availability of information from any place at a given time, while the cyberspace superiority vision is about enabling military actions through cyberspace to deliver non-kinetic effects against an adversary.
Documents like this are aimed at the broader Navy and Marine Corps and “the people who don’t consider this their core business spaces why these things are important — [and] more importantly, why it’s important to their mission,” Cleary said.
“What the vision really talks about is we need to talk about those three things in concert. One doesn’t outweigh the other,” Cleary said, referring to secure, survive and strike. “It’s not to do offensive cyber operations takes away from defensive cyber operations — or to go do Office365 to enable zero-trust structures doesn’t take away from something we’re trying to do in the other two domains.”
The Navy has done a pretty good job on the “secure” front to date, Cleary said. He noted while the SolarWinds intrusion was pretty wide in scope and very sophisticated, the Department of Defense responded quickly once it was discovered.
“We did a pretty good job of getting our hands around that,” he said. The “organizations responding to those things are pretty well-trained, pretty well-equipped within relative orders of magnitude for what they have to do.”
Efforts to secure systems include things like enabling zero trust and identity management.
When it comes to survivability, Cleary explained that the Navy and DOD writ large are under constant attack and thus must be able to fight through to still achieve mission success.
He has previously talked about the need for the Navy to “fight hurt.”
“One of the things we need to think about … whether it’s critical infrastructure or even IT systems, is how do we build those more like we look at building a warship than just an enterprise IT system,” he said last month at the DefenseTalks conference hosted by DefenseScoop. “Those things are going to cost money. If I’m going to build defense critical infrastructure designed to withstand adversary activity, it’s going to be some unique design characteristics that are going to have some unique costs associated with it. I think that’s a realization the Department of the Navy, the Department of Defense needs to come to if we want to have things that are truly survivable.”
He explained that warships are meant to take hits and IT systems must be built with the same mentality.
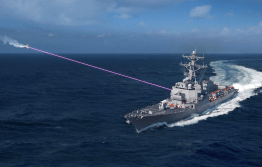
Lastly, when it comes to strike, the vision notes that it would be “unthinkable” to cede domains such as maritime, land or air to the adversary. As such, the Navy must be able and willing to go on the offensive to ensure it does not cede cyberspace.
“It is not enough to statically defend our systems, installations, and networks,” the Navy’s new vision states. “We must dynamically project power in and through cyberspace as part of integrated deterrence. That requires manned, trained, and equipped cyber forces that can defend forward, persistently engage adversaries, and deliver non-kinetic effects at speed. We envision a Navy and Marine Corps performing joint operations in the cyber domain and achieving cyberspace superiority at a combatant commander’s designated time and place.”
While U.S. Cyber Command owns the offensive cyber capabilities within the DOD — and the services conduct offensive cyber operations through Cybercom — Cleary explained to DefenseScoop following his presentation that the Navy is looking at its own version of service-retained capability in line with what other services have done.
Each of the services have begun investing in capabilities and forces for their own offensive cyber, however, that is mostly in the blended electronic warfare or radio frequency-enabled sphere.
“What I will say is the Navy’s looking at, what I’ll use the word, service-retained [forces] — and I think the language we’re going to call them is non-kinetic effects teams,” Cleary told DefenseScoop. “Non-kinetic effects teams will be the Navy’s version of [Marine Expeditionary Force] information groups the Marines have, the mission defense teams the Air Force has” and the Army’s expeditionary cyber teams.
He said the services have missions outside of what they need to present to Cybercom.
“The Navy is still working through what does cyber at sea look like,” he said. “It’s not that the Navy’s not doing these things. It’s just that we are all struggling with what does cyber really mean to our respective service. The Navy is now working through what cyber at sea — a little more specific to Navy missions — really looks like.”
Senior leadership of the Navy is on board with these types of capabilities, but they’ve always fell down the priority list for whatever reason, Cleary said.
“My only reason for existing is to try and drive this higher on priority lists,” he said. “I don’t control resources, nobody really works for me. So I champion an idea, hopefully get the reason for doing it brought and acknowledged to the service — and then once we’re there, help get it resourced.”