Lessons learned from the defense CIOs’ recent West Coast visit to meet with JWCC cloud providers
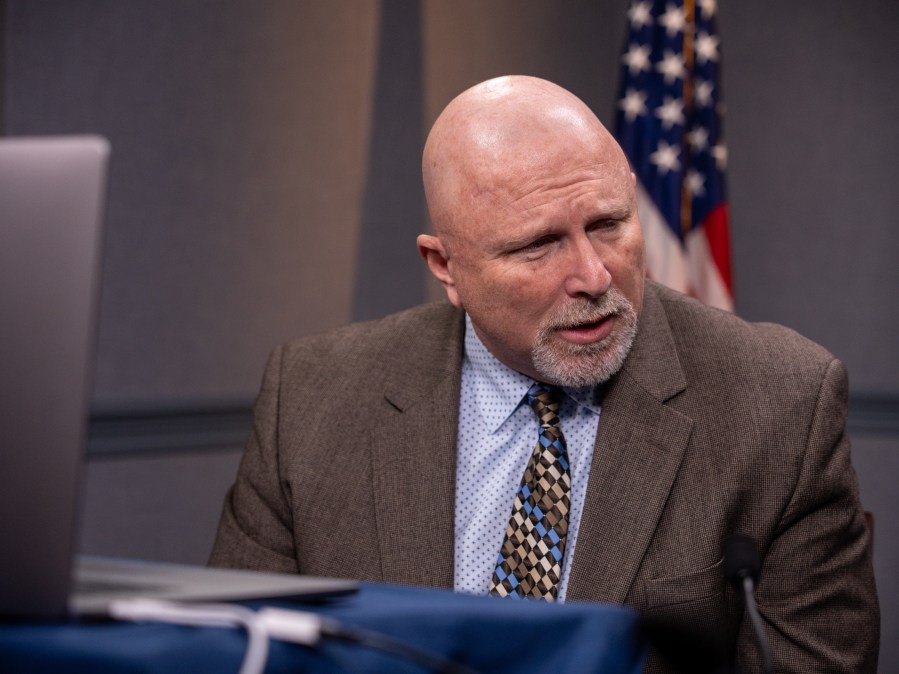
Chief information officers from each of the U.S. military services traveled to the West Coast in February with Dave McKeown, principal deputy CIO of the Defense Department, to visit the four cloud service providers that were awarded spots on the Pentagon’s Joint Warfighting Cloud Capability (JWCC) procurement.
For the most part, the meetings with the four commercial cloud companies — Amazon, Google, Microsoft and Oracle — were opportunities for the CIOs of the DOD, Air Force, Army and Navy, as well as the head of the Defense Information Systems Agency, to touch base and congratulate them on the JWCC partnership and hear about what they were working on.
But it also provided an opportunity to plot out the work they hope to do together and identify any gaps that might exist, McKeown told DefenseScoop in an interview.
“We just recently awarded the JWCC contract, so it was an opportunity for us to meet in person with all of those vendors, congratulate them on being on the contract, talk about where they’re going to take their offering, look at any new and innovative things that they’re planning that we should be sort of taking a look at early, sharing our requirements, things that we’re trying to do,” he said.
Importantly, McKeown explained, it was also “a way for us to understand their pain points in dealing with the federal government and the DOD, as they look to get certified to be a cloud service provider” and the hefty security requirements involved in that.
McKeown acknowledged that communicating security requirements to vendors and helping them navigate them is a large challenge for the department. “I think we probably need to figure out how to express our processes better,” he said.
“To the outside world, I think that’s half of the problem, not knowing what the next steps are and how to get through those steps,” McKeown said. “Like, if you could stand up a concierge service to kind of guide each one of them through the wickets, I think we could cut the time in half to get them through all the checks and balances in order to get their products approved. But a lot of times, it’s sort of discovery learning on their part — they gotta download documents and figure out: ‘Oh, this is where I gotta go next for this next piece.'”
DOD is also open to feedback from those vendors on how the department could do things differently “that would be better, more streamlined, just as secure … instead of the, you know, one-size-fits-all rigidity that we have right now,” McKeown said, while also admitting that “we’ve got to be faster.”
Despite the desire to move faster, recent events involving DOD’s cloud security may have the opposite effect.
Around the same time as the CIOs’ trip to the West Coast, reports surfaced that large numbers of U.S. military emails containing sensitive personnel data were exposed publicly online via a server hosted on Microsoft’s Azure government cloud. As DefenseScoop reported in the wake of that, the exposure has led to DOD CIO John Sherman reviewing the incident and potentially issuing “direct changes in CSP security measures as required based on any findings and recommendations.”
The Pentagon inspector general also in February issued the results of an audit that found military authorizing officials were not thorough enough in reviewing authority to operate documentation, potentially leaving the services “unaware of vulnerabilities and cybersecurity risks associated with operating their systems or storing their data in the authorized commercial [cloud vendors],” the report concluded.
Talking about balancing the benefits of the commercial cloud with the rigid security requirements needed for DOD data, McKeown said: “I don’t think it’s perfect right now as the recent incidents have shown.”
“We’ve got some work to do there on how to shore that up,” he said. “Certainly, we don’t want to get in the business of defending the vendor side of the equation. And one of the reasons why we chose to outsource this was so that they would do all the wrench turning, build the environment, maintain the environment, secure the environment from their side. Anytime we build anything on our side of their platform, we would defend that. But we may need more visibility into their side than we initially thought just so that we can help them do the job of defending the whole entire hypervisor and their management plane behind the cloud service offering.”
But largely, McKeown said, the takeaway from the visit was that the cloud providers were “mostly aware of what our requirements were already and already diligently working on things.”
“Many of them gave us briefings on zero trust, what they’re gonna do there. That tactical edge requirement that we have, you know, they’re already briefing on solutions they’re working there,” he said. “So just knowing that the messaging that we’re putting out as far as our requirements are being clearly heard out there and that they’re acting on it was a really big takeaway.”
It also gave the CIOs a glimpse into the state of the art for technologies like satellite communications, artificial intelligence, zero-trust security and others that the industry leaders are developing.
“I think we’re in a golden era of SATCOM,” McKeown said. “It seemed like a lot of organizations are focusing on that. And how SATCOM can bring us greater bandwidth and resiliency worldwide, which is something, of course, we’re obviously wanting.”
Conversations about ChatGPT and the explosion of AI were also front and center during the meetings. “The really big takeaway there was just how you can use AI to turbocharge just about anything you want to do,” McKeown said.
And on the zero-trust front, the CIOs emphasized to the providers how the cloud can be an accelerant for the department’s adoption of a zero-trust architecture.
“The goal would be a 100% consumable service in their clouds so that there’s little integration work that needs to be done on our side. This is the part of the problem historically: We go out and buy one-off security products, and then it’s our job to integrate them with other solutions to try to achieve a cybersecurity effect,” McKeown said, comparing it to building an F-35 fighter jet. “There’s probably tens of thousands of parts there. We wouldn’t buy each of those parts individually from a vendor and then we the government put them all together to try to make sure that they work, right? We hire an integrator, they build it for us … and then we buy it as a unit. So I think for zero trust, it would be best if we could buy it as a unit and not have people out there on our side trying to be the integrator and miss something.”
He added: “This option holds a great deal of promise for us if all we have to do is kind of move neighborhoods, bring your data, bring your services into this already zero-trusted environment and plug it in. It can be a game changer for us.”






