Austin orders Pentagon CIO to ‘immediately’ issue new guidance for protecting classified information
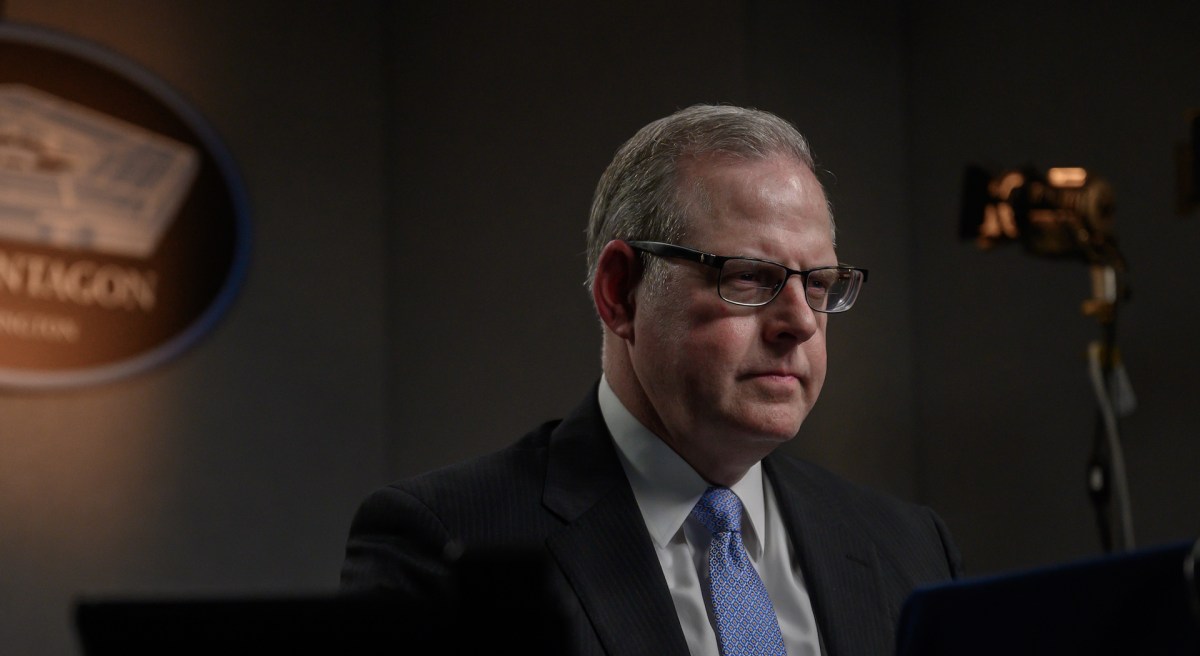
Department of Defense Chief Information Officer John Sherman has been directed to “immediately” issue new guidance to help the Pentagon better protect classified information, according to a new memo from Secretary of Defense Lloyd Austin.
Austin last week ordered a “comprehensive” 45-day review of the department’s security programs, policies and procedures for protecting sensitive information. The new directives are being issued in the wake of the recent online posting of troves of classified documents and the arrest of Air Force National Guard member Jack Teixeira in connection with the Justice Department’s investigation into the incident.
However, the Pentagon chief isn’t waiting for the 45-day review to be completed before new measures are taken to better protect classified information.
“The DoD CIO will also immediately issue additional guidance for the Department. These actions and measures may include, but will not be limited to: restriction or deletion of distribution lists on classified computer networks, allowing limited physical and electronic access to certain intelligence products, granting printing privileges on the Joint Worldwide Intelligence Communications System by exception, requiring proper information handling procedures including encryption of emails, and increasing inspections when people enter and exit Sensitive Compartmented Information Facilities,” Austin said in the new memo, which was disseminated to DOD personnel on Monday and distributed to reporters Tuesday morning.
The undersecretary of defense for intelligence and security is also expected to coordinate with Sherman and the director of administration and management, in leading the 45-day review of DOD security programs, policies and procedures.
In the interim, Defense Department components have been tasked with reviewing and assessing their adherence to standards for protecting classified national security information. The deadline for reporting their findings to the I&S office is May 2.
“Adverse security incidents are a stark reminder that adherence to required security procedures underpin all aspects of the Department of Defense (DoD) mission, and we must continually reinforce these requirements to keep pace with evolving threats. It is therefore essential to carefully examine the sufficiency of, and compliance with, all security policies and procedures,” Austin wrote in the memo.
DOD components must ensure their organizations adhere to a list of department standards regarding the handling of classified information, including those related to accountability; safeguarding; storage and destruction; transmission and transportation; security education and training; reporting of security incidents involving classified information; cybersecurity protocols; and transmission on private sector communications channels expressly prohibited, he added.
Based on the outcome of the review and other findings, the undersecretary for I&S, director of administration and management, and the CIO will advise Austin “on any necessary security policy changes, including those related to the aforementioned standards and will identify forward any enhanced requirements for those with access to our most sensitive systems, information, and facilities,” per the memo.
Austin has also directed Defense Department components to have their counterintelligence and security personnel provide refresher training to the workforce.
“This training should address the risks and consequences of unauthorized disclosures, which may include, administrative penalties, such as termination of employment, or criminal prosecution, as appropriate,” he said in the memo.
With regard to cybersecurity protocols and electronic transmission, the memo notes that DOD personnel are only supposed to transmit classified national security information over secure communications networks that have been approved for such transmissions at the specified level of classification.
Defense Department components must also immediately review their adherence to existing policies and guidance to ensure compliance with system access controls, auditability, and user activity monitoring on classified networks, and adhere to the principle of “least privilege” access to classified data, per the memo.
Austin also noted that electronic messaging services — including private social media accounts or groups, and messaging applications such as WhatsApp, Signal and others — that aren’t controlled by the Pentagon are not authorized to process non-public DOD information.






