Don’t look now: The next generation of cybersecurity threats is already here
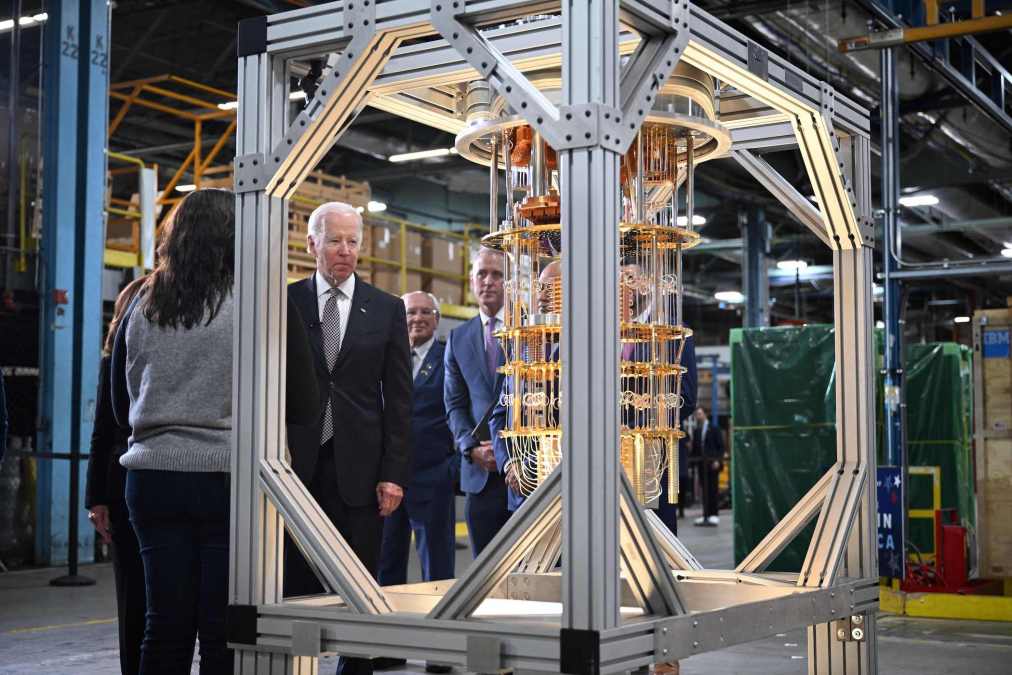
Late last year, President Biden signed the Quantum Computing Cybersecurity Preparedness Act (QCCSP) into law. The act directs the U.S. Office of Management and Budget to prioritize the challenging and resource-intensive task of migrating federal IT systems to quantum-resistant cryptography and to send Congress a report outlining its strategy to do so by December 2023. Though the legislation was passed without much fanfare, it represents a significant step toward securing our nation’s future.
While it may be some time before quantum computers are able to break today’s encryption protocols, this is not a future problem–it’s already here. Nation-states and other adversaries are conducting what are known as “Store Now, Decrypt Later” attacks — stealing encrypted data and housing it on their own servers to decrypt and exploit later. These attacks target U.S. and allied government agencies as well as companies in vital industries such as defense contracting, technology, financial services, telecommunications, healthcare, pharmaceuticals, energy, and more.
Any organization that relies on data security to fulfill its mission should feel a sense of urgency. At risk are critical infrastructure and the personal data of everyday consumers, including passwords, personal health, and financial information. Specifically for the Department of Defense, data at risk could include classified intelligence, the details of treaty negotiations, military strategy and decision-making processes, weapon designs, training protocol, personnel information, or the names and locations of high-value targets and operatives.
It will be too late if the U.S. waits for more capable quantum computers before taking significant steps to address this threat to secure cryptography. Once scaled quantum computers are stable, they will be able to crack nearly all existing security codes and protocols in hours, if not minutes. Most national security data without quantum-resistant cryptographic protocols that are stored by bad actors today will have enduring value even if encrypted a decade or more from now. To protect against this, The National Security Agency set a 2035 deadline for the adoption of post-quantum cryptography (PQC) in national security IT systems, an ambitious goal that the Defense Information Systems Agency will be responsible to execute.
The National Institute of Standards and Technology has released a set of validated PQC algorithms that form the foundation of quantum-safe encryption. These algorithms are the result of a rigorous, six-year effort by a group of stakeholders from 25 countries and offer DISA the clarity necessary to migrate critical systems and data to PQC.
PQC adoption hurdles
The process of implementing PQC protocols across the DoD is complex and will take time, but the effort is attainable thanks to unprecedented public-private cooperation. In 2022, NIST’s National Cybersecurity Center of Excellence (NCCoE) introduced its Migration to Post-Quantum Cryptography project, which includes an international consortium of 17 companies to help organizations transition to PQC. While that is reason for optimism, many hurdles remain that prevent DOD’s timely adoption of PQC.
First, DOD leaders are contending with an increasingly complex security environment that includes the rise of adversaries with capabilities and capacity we’ve not seen for generations–and some capabilities we’ve never seen. The multipolar world is here and an important aspect of maintaining America’s place in global affairs will be setting the pace with emerging and revolutionary technologies–such as evolving data encryption standards–that have far-reaching implications for national security, including warfighting.
Another challenge is that many emerging disciplines such as quantum technology remain poorly understood and daunting to tackle. The security implications also remain nebulous. Those in DOD who are fully aware of the threat quantum computers present are also overwhelmed when considering where their PQC migration should begin.
A way forward
An executable and productive way ahead is to reframe PQC migration efforts as a set of problems that can be solved in stages. Many experts recommend the first stage in any PQC migration should be a cryptographic inventory and vulnerability assessment, which would require more modest amounts of initial funding to begin. This discovery process takes several months or more but is essential before migration, policy management, and enforcement can begin. Many industry players, such as those identified by NCCoE, stand ready to partner with DISA to tally cryptographic inventories, develop migration road maps, and project annual costs. These are steps that can be taken right away.
Lastly, DOD IT leaders must remember that “cryptographic agility” — the ability of a cybersecurity system to rapidly adapt new cryptographic algorithms — will be an important element of PQC migration since the process of securing data from quantum threats will be continuous and dynamic. Applying the modular, stepped approach outlined above would help achieve and maintain the agility needed to address future cyber threats. An agile IT architecture must maintain an inventory of cryptographic components and update them as necessary to stay current with the latest standards and best practices.
Strong DOD leadership has made great strides toward Zero Trust IT architectures that continuously validate each stage of digital interactions. This is a good start, and part of achieving cryptographic agility is that Zero Trust will need to integrate and complement PQC.
But as the QCCSP Act highlights, there is still an urgent need for DOD and all organizations that depend on data security to begin the PQC migration process to protect critical data and infrastructure — now. The NSA anticipates new cryptography will take 20 years or more to be fully deployed across national security systems. We must do better than that. We’re not alone here — China already claims to have a practical quantum computer and an algorithm that can break public-key encryption.
The race is on, and there’s not a moment to lose.
Adm. (Ret.) John Richardson was the former Chief of Naval Operations for the U.S. Navy. He is an advisory board member for quantum and AI company Sandbox AQ.






