Sec. Austin issues new guidance to streamline Pentagon’s protection of classified information
A recent review of the Defense Department’s security programs, policies and procedures is leading to 14 new directives that aim to streamline how the Pentagon handles classified national security information, according to a new memo from Secretary of Defense Lloyd Austin.
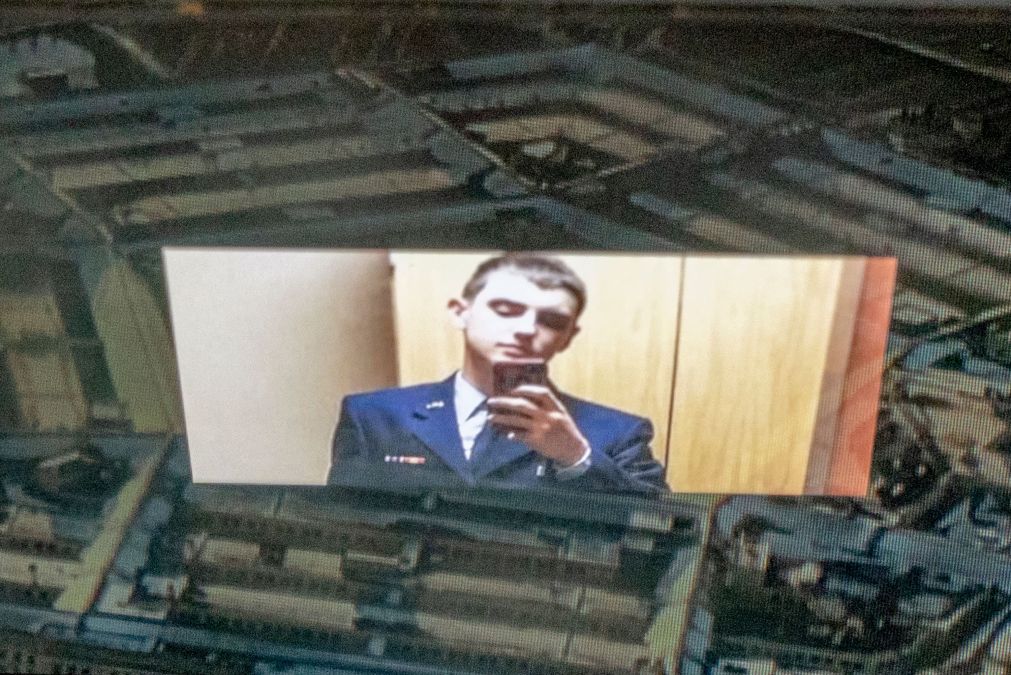
In April, Austin ordered Undersecretary of Defense for Intelligence and Security Ronald Moultrie to lead the 45-day review after multiple classified documents were published and widely shared online. U.S. federal agents later arrested Air Force National Guard member Jack Teixeira in connection with the Justice Department’s investigation of the leaked documents, which according to the DOJ included sensitive details about Ukrainian military operations and other classified national security and intelligence information.
Based on the findings of the review, Austin has now issued guidance to senior leaders across the Pentagon on required actions to take in the near- and medium-term in order to improve security and accountability measures.
“This review found that the overwhelming majority of DoD personnel with access to CNSI are trustworthy, and that all DoD Components demonstrate a broad commitment to security,” Austin said in the memo, which was sent to Pentagon personnel June 30 and shared with reporters Wednesday. “However, the review identified areas where we can and must improve accountability measures to prevent the compromise of CNSI, to include addressing insider threats.”
According to a DOD fact sheet, the 50-question self-assessment was sent to Defense Department components and included questions about personnel security, information safeguarding and accountability, physical security and education and training posture.
During a media roundtable Wednesday, a senior defense official told reporters the review team found lack of clarity in the Pentagon’s policies for handling classified information that have created inconsistencies throughout the department.
“We have a widespread population, as well as a constellation of facilities,” the official said. “So, I think for us, as the department’s population of cleared personnel and the number of facilities have grown over the past few years, it has underscored the need to have a comprehensive and evolving security in-depth posture.”
In the memo, Austin has directed all Defense Department components to complete a number of actions to guarantee compliance and accountability for those handling classified information. Component heads will be required to review current policies and create corrective action plans that ensure all department personnel are accounted for in security information systems and assigned to a security management office (SMO) by the end of August.
Any DOD components not part of the intelligence community “will validate the continuing need for their personnel to have access to Sensitive Compartmented Information (SCI) and ensure personnel who require such access have a valid SCI non-disclosure agreement on file with their assigned SMO” by the end of September, the memo stated.
Austin is also directing the undersecretary for I&S, in coordination with Department of Defense Chief Information Officer John Sherman, to establish a Joint Management Office for Insider Threat and Cyber Capabilities within 90 days of the memo’s publication. The office will oversee user activity monitoring activities, such as security being notified of any personnel conducting unusual activity on a DOD network, the senior defense official said.
The undersecretary for I&S, CIO and other stakeholders must also “implement a phased approach to increase accountability, manage access, and increase security to classified data by August 28, 2023,” he said in the memo.
That recommendation is focused on optimizing the Pentagon’s “need-to-know” policies and procedures for its electronic ecosystem, which includes how it validates which documents can be accessed online and what credentials an individual needs on their “digital passport” to view them, the senior defense official said.
With regards to the physical infrastructure where classified information is processed and disseminated, the memo requires the undersecretary for I&S to develop and maintain a new centralized tracking system for sensitive compartmented information facilities (SCIF) and special access program facilities (SAPF).
New policy guidance that reinforces the prohibiting use of personal and portable electronic devices within SCIFs and SAPFs must also be implemented, and all Defense Department components will also be required to create programs for capabilities that can detect electronic devices in such facilities.
In addition, the memo tasks the DCSA, CIO and Chief Data and Artificial Intelligence Officer at the Pentagon to optimize “security information technology systems for information sharing and informed access decisions in a manner that is supported by data reporting and analysis in Advana or other system of record.”
As it implements the new directives, the Pentagon will work to prevent actions that could cause “overcorrection” and prevent it from executing the department’s mission, the fact sheet noted.
“This is to ensure that we’re appropriately calibrating our response to make sure that we do not inhibit the department’s ability to operate with both other components within the department, as well as our interagency partners,” the senior defense official said. “This is about making sure we’re validating need-to-know — not necessarily turning off access.”






